Core Components of a Cloud Security Framework
A cloud security framework is a set of tools, policies, procedures, and technology designed to protect data, applications, and infrastructure resources. As organizations increase their cloud footprint, the need for a cloud security framework increases.
A robust cloud security framework provides a structured approach for identifying, assessing, and mitigating risks and vulnerabilities across cloud applications and infrastructure. As exploits against vulnerabilities like Log4Shell have demonstrated, the need to adopt the right tools to maintain a strong security posture has never been more critical.
A cloud security framework also aids organizations in achieving and satisfying their compliance and regulatory requirements and industry standards. A framework can guide in implementing suitable security controllers.
This article will explore four essential cloud security framework components typically available from public cloud providers and how organizations can use them to improve their overall security posture.
Summary of key cloud security framework concepts
The table below summarizes the four cloud security framework components this article will explore in more detail.
| Concept | Details |
|---|---|
| Identity and Access Management (IAM) | Deals with the management of user authentication, authorization, and identity management. |
| Data protection and encryption | Safeguards sensitive information with encryption tools and ensures keys are protected. |
| Network security | Focuses on securing the network infrastructure using firewalls, IDPS and VPNs. |
| Incident response and recovery | Establishes incident response plans that include roles and responsibilities and monitoring capabilities. |
Cloud security framework component #1: Identity and Access Management (IAM)
In the current landscape of IT security and cloud computing, IAM plays a crucial role in securing cloud environments by providing a vigorous framework for managing users, groups, and service account identities.
IAM also controls and manages resource access by ensuring that only authorized users or service account entities can access cloud services.
Multi-factor authentication (MFA)
One of IAM's core functions is implementing strong authentication mechanisms to verify users' identities before granting access to infrastructure resources.
For example, multi-factor authentication (MFA) — a security principle requiring users to provide two or more factors to verify their identity — can significantly reduce the risk of unauthorized access to their infrastructure and applications.
Factors that can be used in an MFA implementation are:
- Something the user has (e.g., smartphone or hardware token)
- Something the user knows (e.g., username and password)
- Something the user is (e.g., fingerprint or facial recognition)
In some advanced configurations, a conditional MFA requires users to use MFA based on a predetermined condition, such as a user’s location.
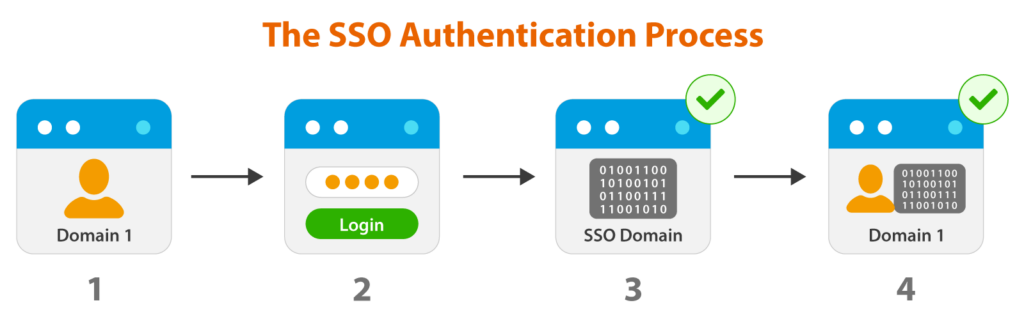
Single sign-on (SSO)
With IAM, organizations can facilitate single Sign-On (SSO) capabilities and allow users to log in and access multiple applications using a single username and password set. SSO also eliminates the need to remember multiple login credentials and centralizes the authentication process across various apps into a single identity provider.
To achieve strong authentication security, MFA and SSO can be used together with conditional MFA that is triggered when SSO is used across multiple platforms.
The SSO Authentication Process
How to effectively implement user and access management
Effective user and access management is another core component of IAM and involves using controls, policies and processes to manage the identities of users, groups and service accounts.
Follow the principle of least privilege
User provisioning gives new users the appropriate access privileges to resources and applications when they join an organization. Once a user leaves the organization, the reverse order takes place using de-provisioning, where access is revoked.
Standardize user provisioning and de-provisioning
Organizations reduce the risk of orphaned accounts in their identity directory by using a proper process to provision and deprovision users. To read about the Azure AD user provisioning process, reference this Microsoft article.
Use role-based access control (RBAC)
RBAC is a popular approach to managing access and considers best practices according to industry standards. It gives organizations a structured approach to assigning access permissions based on user roles and responsibilities.
A role is associated with predefined permissions allowing users to do their specific job function. It simplifies access to infrastructure and applications by reducing the overhead configuration of custom access permissions.
Cloud security framework component #2: Data protection and encryption
Data protection is the process of an organization implementing strategies and using tools to safeguard sensitive information during transmission and storage. The design must include a process that maintains data integrity and availability.
Encryption is the process that ensures data is safe and protected at all times. Data can be exposed to many risks in the cloud, like unauthorized access and data breaches.
Encryption strategies for data at rest and in transit
Encrypting data at rest and in transit are two crucial practices for security-conscious organizations.
Encrypting data at rest involves using encryption protocols and algorithms to encrypt data while it is stored in any storage medium (e.g., a database or a network drive).
When data at rest is enabled, it can use the following encryption methods:
- Full disk encryption – The entire disk that holds the data is encrypted, including the operating system.
- File-level encryption – Only specific files and folders are being encrypted and not the entire disk.
- Database encryption – This method encrypts data inside a database.
A good example of encrypting data at rest is Azure Blob storage data at rest encryption, where organizations have the choice to use their private keys to encrypt the data rather than Azure private keys (default).
Azure users can also choose between Microsoft-managed or customer-managed keys. Microsoft-managed means that Microsoft will store, generate and store the keys. With customer-managed keys, the customer needs to store, generate and store the keys.
Encrypting data in transit involves implementing encryption for data transferred across a network to reduce the risk of threats like eavesdropping.
Common examples of data in transit encryption include:
- Secure Socket Layer (SSL/TLS) – Data encryption for web protocols like HTTPS.
- Virtual Private Network (VPN) – Encryption tunnel between multiple networks (Site to Site or Point to Site VPN)
- Secure File Transfer Protocol (SFTP) – Protect file transfer between clients and storage server.
Encryption protocols and algorithms
Once a strategy is selected, the next step is to use a suitable encryption protocol and algorithm. The most popular protocols are:
- Advanced Encryption Standard (AES) – This symmetric encryption algorithm is used for strong encryption.
- Rivest-Shamir-Adleman (RSA) – This asymmetric encryption algorithm is used for data exchange, digital signatures and secure communication.
Key management best practices
Key management is the process of managing the encryption keys an organization uses to decrypt and encrypt data. When managing encryption keys, organizations should follow these five best practices:
- Generate new keys securely – When generating new keys, the process has to happen using a safe environment and a defined process.
- Take precautions with key storage – Storage of keys needs to include an offline storage component and physical location to store the keys.
- Use secure protocols and channels to distribute keys – When distributing security keys to stakeholders, the process has to be safe and secure using secure protocols.
- Rotate keys regularly – Keys must be rotated every 6 to 24 months and changed on all systems.
- Revoke compromised keys – Expired or compromised keys must be revoked.
Cloud security framework component #3: Network security
Securing a cloud network is essential when protecting cloud resources, applications, and data from threats and malicious attacks. A cloud network must protect against unauthorized access, data breaches, and malicious activities.
Implementing the following security measures can help any organization maintain the integrity, confidentiality and availability of a cloud environment.
Network segmentation and firewalls
With network segmentation and firewalls, an organization divides its cloud infrastructure into isolated networks. This creates a barrier between different resources and workloads and limits the potential impact of security incidents.
Once implemented, network segmentation allows organizations to control specific access to each segment and mitigate risks like data breaches and unauthorized access.
The firewall component's job in the segmentation process is to enforce security access policies and inspect network traffic.
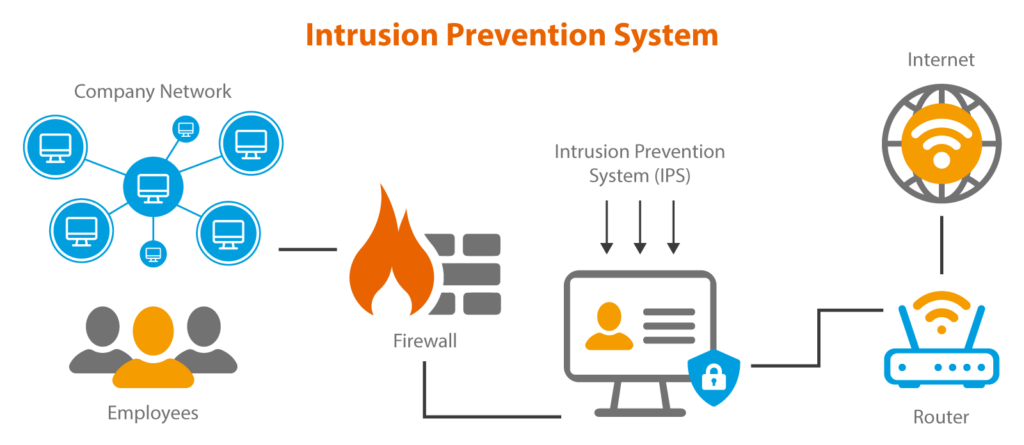
Intrusion detection and prevention systems (IDS/IPS)
IDS solutions are network and software solutions that detect and stop network-based security threats. The IDS component’s job is to monitor network traffic and identify abnormal activities and security breaches.
The IPS's job is to block and prevent the discovered threats using solutions like behavioral analysis, signature-based detection and anomaly detection.
Intrusion Prevention System
Monitoring and logging for network security
The third component to protect a cloud network is a continuous monitoring and logging solution. This tool continuously detects and logs compliance changes and security policies to form a critical part of your security framework.
Most cloud providers have native tools that can provide monitoring and logging capabilities. Enterprises can also leverage platforms like CoreStack to support their cloud governance activities while still using native tools for operational activities.
Cloud security framework component #4: Incident response and recovery
The last section of developing a robust cloud security framework is an incident response and recovery system that allows an organization to respond to security incidents and data breaches and maintain optimal business operations. An efficient and robust incident response and recovery plan is essential for minimizing the impact of incidents across a cloud infrastructure.
Developing an incident response plan
An effective incident detection and response plan is mainly measured by the time it takes to detect and respond to security incidents. The only way to respond quickly and effectively to incidents is to use robust monitoring solutions that provide real-time analysis.
Solutions like IDS, security information and event management (SIEM), log analysis, and CoreStack’s next-gen SecOps tool can reduce the time it takes to detect and respond to security incidents and changes to the cloud infrastructure.
Post-incident analysis and lessons learned
Once an incident has been resolved, conducting a post-incident review and analysis is critical for continuous improvement of the incident and response process.
By analyzing the root cause and putting measures in place to prevent similar incidents, an organization improves its response capabilities and the process of handling similar incidents in the future,
Continuous improvement and updates to the security framework
To complement the above steps, a system that allows an organization to improve its capabilities and evolve continuously is critical in developing a cloud security framework.
The best way to maintain a continuous improvement strategy is to foster a culture that allows progress by regularly reviewing and updating security policies and procedures and implementing recommendations promptly.
|
Platform
|
Provisioning Automation |
Security Management |
Cost Management |
Regulatory Compliance |
Powered by Artificial Intelligence |
Native Hybrid Cloud Support
|
|---|---|---|---|---|---|---|
|
Cloud Native Tools |
✔
|
✔
|
✔
|
|||
|
CoreStack
|
✔
|
✔
|
✔
|
✔
|
✔
|
✔
|
Conclusion
A robust cloud security framework is essential in any cloud environment, and its primary purpose is to ensure applications, data and core infrastructure is always protected. By applying the concepts and best practices in this article, organizations can reduce their exposure to security risk.
Organizations can implement a cloud security framework using native tools offered by their cloud provider or a comprehensive governance platform like CoreStack, which offers advanced capabilities like access governance posture, visibility and control over resources, compliance with security standards, and efficient cloud resource management.