Achieving Cloud Compliance in a Multi-Cloud World
Cloud technology practitioners have indicated that the biggest challenges in using cloud computing technology are related to security. However, 60% of the world’s corporate data is stored in the cloud, and 90% of large organizations have adopted a multi-cloud infrastructure, according to 2023 cloud computing stats.
Cloud compliance is all about aligning your organization’s use of the cloud with regulatory, industry, customer, and internal standards. By following cloud compliance recommendations, your organization will have better assurance that your cloud environment is secure and aligned with security and operational best practices. Demonstrating your cloud compliance might be a requirement for your industry, and failing to meet the required standards may have legal and financial ramifications.
This article will provide an overview of cloud compliance, with a focus on how a cloud compliance management platform, particularly for multi-cloud operations, can help your organization benchmark its compliance posture.
Summary of key cloud compliance concepts
We recommend viewing cloud compliance as a continuous cycle that involves the following stages and associated questions.
| Stage | Compliance questions |
|---|---|
| Identify |
|
| Detect |
|
| Remediate |
|
| Continuous |
|
Compliance cycle
The first three stages above form a continuous compliance cycle, as illustrated below, and we will consider each stage in order. A cloud compliance management platform can help with all stages of this compliance cycle. In multi-cloud scenarios, third-party cloud compliance management platforms can simplify aggregation, ensure the consistency of compliance reporting, and streamline remediation actions.
The image shows a compliance cycle with three stages: identify, detect, and remediate
Identify
The first stage of a compliance cycle is to identify the compliance frameworks that your organization is targeting. These may be specific to the industry that your organization works in, mandated by your internal cloud governance framework, or driven by your customer’s requirements.
Legal and regulatory compliance
These are local and international laws that may be relevant to your organization. For example, the Health Insurance Portability and Accountability Act (HIPAA) is concerned with how patient data is disclosed, managed, stored, and viewed. If your organization handles healthcare data, it must comply with HIPAA. This starts with using a public cloud provider that is HIPAA-compliant.
Another example is the EU’s General Data Protection Regulation (GDPR). For example, if your organization is using EU consumer data, adhering to GDPR may require controls to be in place to delete their data. If your organization is handling payments, then compliance with the Payment Card Industry Data Security Standard (PCI DSS) will be required.
You should ensure that any third-party compliance management platform supports the legal and regulatory compliance required by your organization. Some compliance platforms have linked the common policies between the compliance standards. For example, if a common policy exists in both the HIPAA and GDPR standards, then they are linked. During the identification stage, this can help with understanding the relationships between compliance standards.
An example of a compliance platform that shows links between compliance standards
Security-centric frameworks
These frameworks help your organization identify actionable defense practices to improve your cloud environment security posture. We recommend that your cloud environment be benchmarked against frameworks like the following:
- ISO 27001: Standard for information security management systems (ISMS) and their requirements
- NIST Cybersecurity Framework: Provides a common language and methodology for managing cybersecurity risk
Well-architected frameworks
Cloud providers commonly provide guidance on how to use their services properly, and a multi-cloud management system can check if you are following the advice. Examples include the following:
- Amazon Web Services Well-Architected Framework
- Azure Well-Architected Framework
- Google Cloud Adoption Framework
Compliance management platform frameworks
Some management platforms have their own well-architected frameworks that can provide additional best practices to adopt. In multi-cloud environments, it can become time-consuming to review each cloud-provider-specific framework. A multi-cloud compliance management platform can streamline assessment by providing a single well-architected framework that is vendor-agnostic. This also allows best practices in common areas, such as operations, security, and cost, to be grouped together.
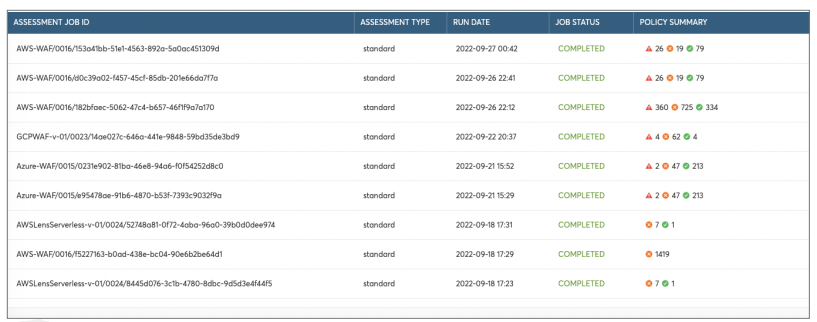
Output from a well-architected framework assessment against a multi-cloud environment
Cloud compliance frameworks
These are frameworks developed explicitly for cloud providers and organizations using cloud services. Examples include the following:
- Cloud Security Alliance Controls Matrix: A cybersecurity control framework for cloud computing
- FedRAMP: Provides a standardized approach to security authorizations for cloud service offerings for the US federal government
Shared responsibility
When the cloud provider says that its services are HIPAA-compliant, this means that the underlying infrastructure is secure and that it provides tools that can ensure compliance. Your organization is still responsible for using the compliant tools appropriately and putting in place monitoring and reporting. Cloud providers often refer to this as the shared responsibility model.
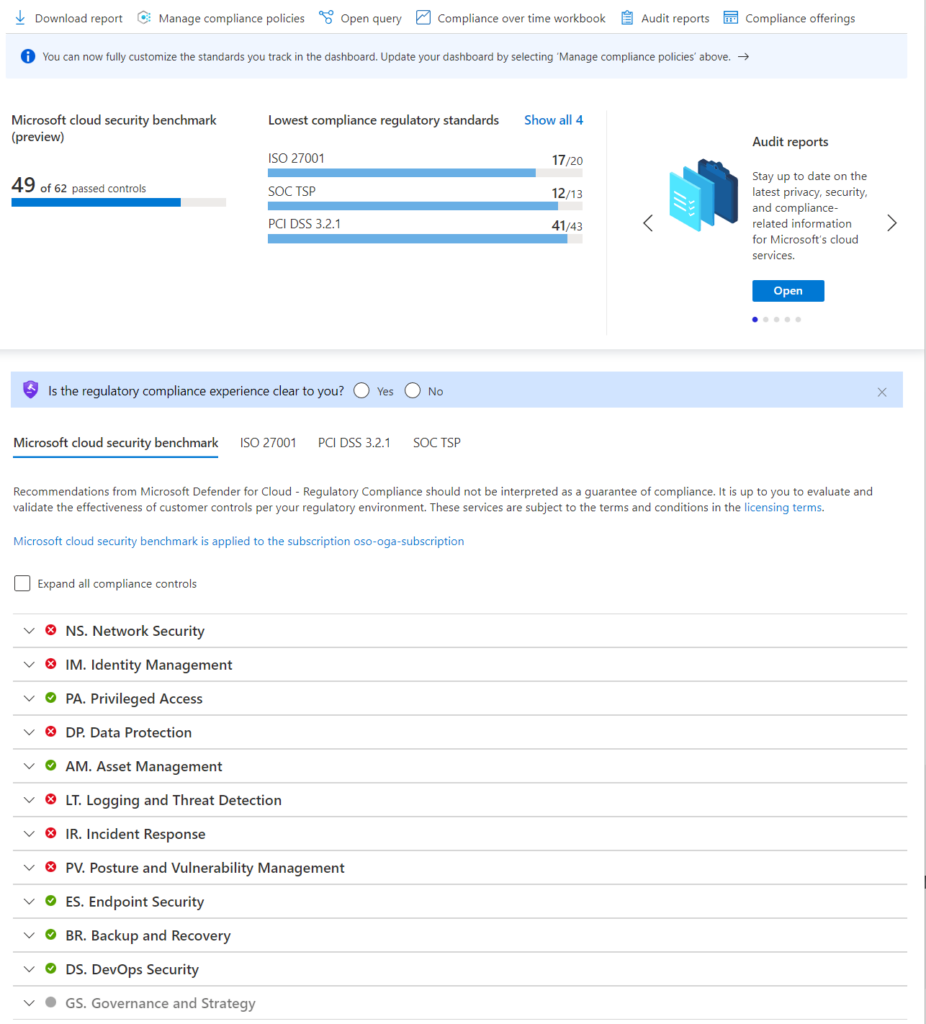
Detect
The major cloud providers have built-in detection for regulatory compliance. For example, Azure Microsoft Defender for Cloud has a regulatory compliance dashboard. It has support for adding additional regulatory standards, and you can also onboard cloud accounts from AWS and GCP. However, developing new features is more likely to prioritize Azure than AWS and GCP since Azure Microsoft Defender for Cloud is a Microsoft product.
Microsoft Defender for Cloud regulatory compliance dashboard
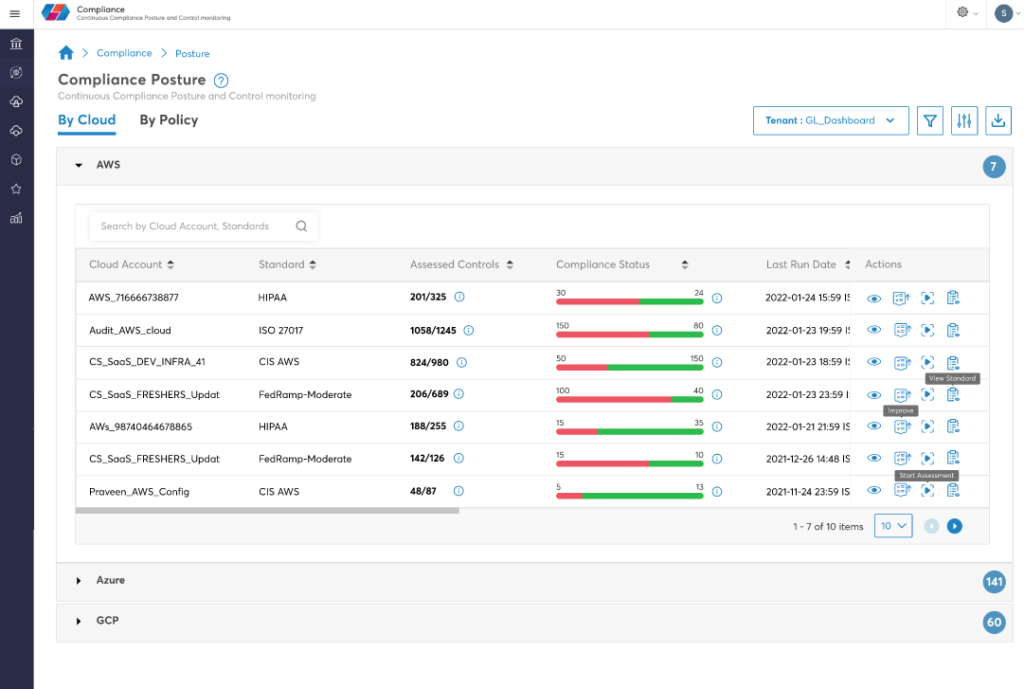
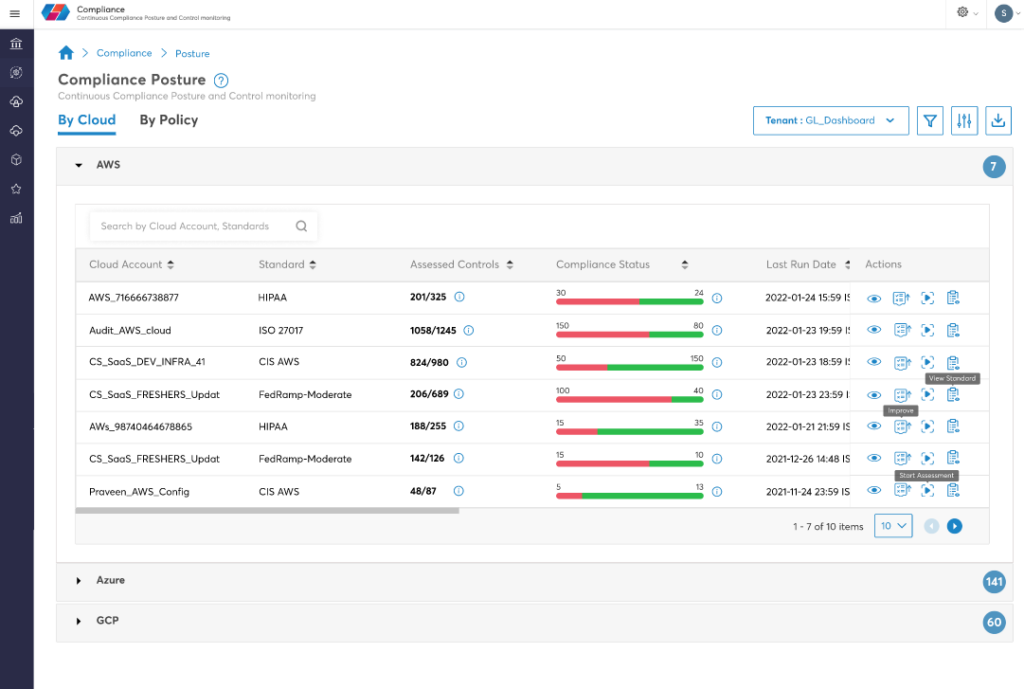
In a multi-cloud environment, third-party multi-cloud management platforms are likely to improve the efficiency of compliance checks by offering consistent functionality across each supported cloud provider. The image below shows an example of a compliance posture summary from a third-party management platform that presents a consistent summary for each major cloud provider.
An example of a consistent compliance posture summary from a third-party multi-cloud management platform
In a multi-cloud environment, running compliance checks can be a time-consuming task. Using a multi-cloud management platform that improves the efficiency of compliance checks will help your organization detect compliance violations more quickly. This is particularly useful for agile development methodologies. If detecting compliance violations is slow, it will not happen regularly and will become a burden, rather than an integrated part of the DevOps cycle.
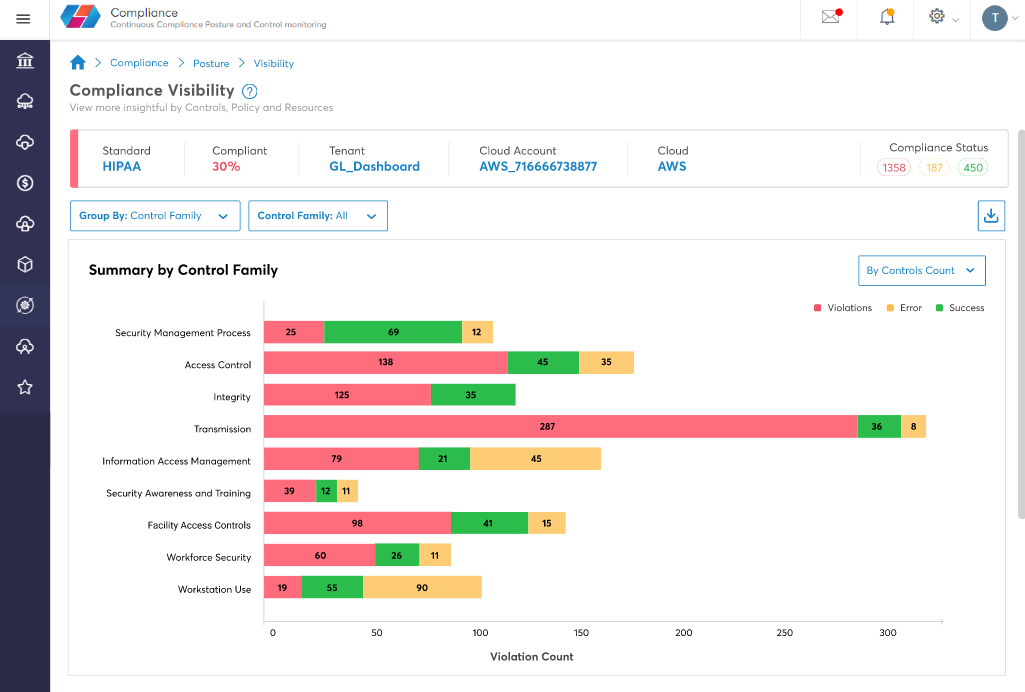
A summary of the compliance posture for different controls
Some management platforms provide integrations to other monitoring tools, such as Anomaly Detector, Nessus Qualys, and Zabbix. These integrations help extend the capabilities of the management platform and enable metrics from these tools to be aggregated.
Remediate
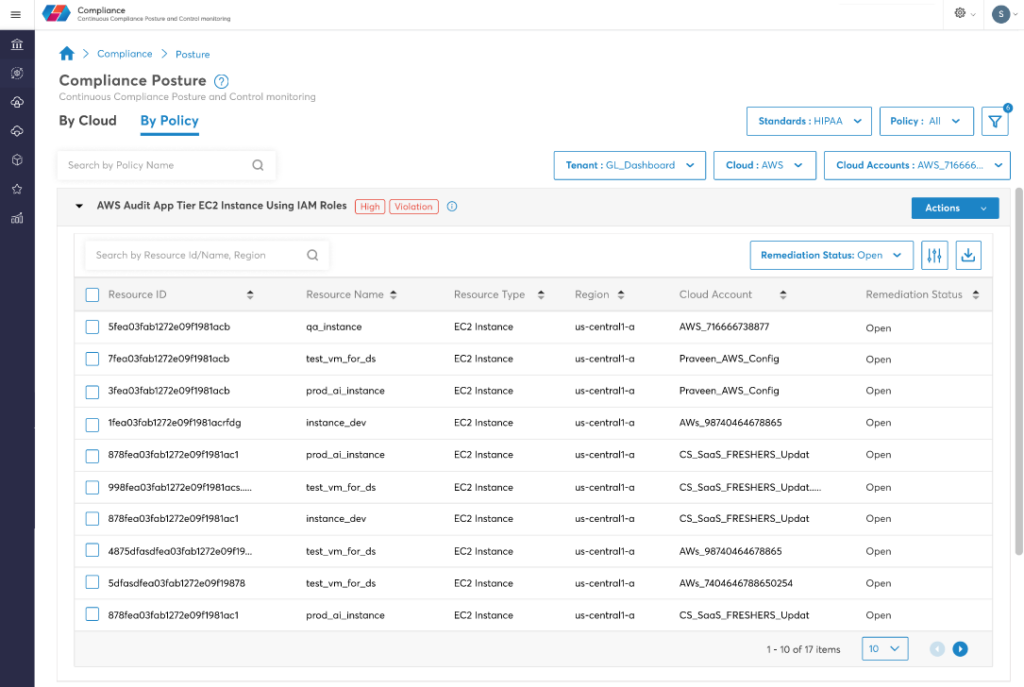
The final stage in the compliance cycle is to remediate the detected compliance violations. The compliance management platform should provide a consolidated compliance posture dashboard, as shown in the image below. From this, it is possible to drill down into a specific cloud account or compliance standard to see the compliance status in more detail.
Compliance posture by cloud account
The compliance platform will provide a table of affected resources and the remediation status. The image below shows an example of resources that have an open remediation status. Each should be addressed with one of the following actions: fix, exempt, or ignore.
Further integrations are possible with IT service management (ITSM) tools like Jira, ServiceNow, and BMC Remedy. This enables compliance policy violations to be created as incidents within these tools; where appropriate, automated remediation workflows can remediate compliance violations automatically.
Compliance posture by policy, in this case, HIPAA
| Action | Description |
|---|---|
| Fix | Change the noncompliant resource to be compliant.
As mentioned earlier, a multi-cloud management platform can automatically fix some compliance violations through integration with third-party tools like Jira, ServiceNow, or BMC Remedy. A useful feature of some compliance platforms is that they can understand that policies are common across multiple standards. This means that fixing a noncompliant resource will be reflected across multiple standards. |
| Exempt | This will ensure that a noncompliant resource is not listed in the future.
Adding exemptions should not be your default behavior, and it is important to add a description of why the resource is exempt or to categorize the exemption reason. Your description should be detailed enough for you to revisit it in the future and understand the reason for the exemption. An example of a common exemption is resources that have access to public IP addresses. These resources are likely to be flagged as being noncompliant, but your application may require this. |
| Ignore | This is not a recommended action.
Tagging of resources can help those reviewing compliance to escalate issues to the appropriate department in the organization. Your cloud governance should include minimum requirements for resource tagging. These tags should let you identify who owns the resource, whether it is in production, and whether it contains sensitive data. Having this information will help you prioritize noncompliant resources. For example, if a noncompliant resource is tagged environment: development and risk:non-confidential, then ignoring the compliance violation is a valid action. |
Continuous
Events like evaluating a new cloud service, developing a new application, or entering a new market are likely to prompt a review of your organization’s compliance. However, a compliance management platform that streamlines the compliance cycle will help embed a culture of continuous compliance within your organization. Rather than just relying on events to prompt you to review compliance, it should become an integrated part of your DevOps cycle.
To achieve this, the compliance cycle needs to be as efficient as possible. For example, by default, Azure Policy evaluates compliance data every 24 hours. Picking a compliance management platform that performs automated compliance testing more quickly will help your teams embed compliance testing into their development cycles.
|
Platform
|
Provisioning Automation |
Security Management |
Cost Management |
Regulatory Compliance |
Powered by Artificial Intelligence |
Native Hybrid Cloud Support
|
|---|---|---|---|---|---|---|
|
Azure Native Tools |
✔
|
✔
|
✔
|
|||
|
CoreStack
|
✔
|
✔
|
✔
|
✔
|
✔
|
✔
|
Summary of key compliance concepts
A cloud compliance management platform will ensure that your multi-cloud environment is aligned with your organization’s requirements for regulatory, industry, customer, and internal standards.
You should view cloud compliance as a continuous cycle, which starts by identifying compliance requirements, then detecting compliance violations, and finally remediating resources that are noncompliant. However, running compliance tests to detect compliance issues can be complex and time-consuming, especially in a multi-cloud environment.
A holistic approach to cloud compliance is crucial for overcoming these complexities. With an assurance to uphold a strong and secure cloud environment, CoreStack facilitates compliance with prominent industry standards such as ISO, FedRAMP, NIST, HIPAA, PCI-DSS, AWS CIS, and Well Architected Framework.
CoreStack’s AI-powered multi-cloud governance solution helps enterprises harness the full potential of cloud computing while enabling continuous and autonomous cloud governance at scale. With automatic baselining of cloud resources and identifying drifts and deviations for compliance and governance, CoreStack can play a pivotal role in empowering your business to achieve its objectives.